Network Security is an increasing concern for any Business and is the reason why major Vendors like Cisco are upping their game with technologies like Advanced Malware Protection (AMP). AMP technology now comes with a new tool called Cisco AMP Unity, a cloud service for enterprise network management for inbound and outbound connections.
In a world full of lurking threats, there is no one-stop solution to network security. To network professional’s securing an endpoint could potentially save all network users from intrusions over inbound or even outbound connections. Therefore, this new cloud-oriented approach to network security makes enterprise security easier, easy to test/deploy and budget-friendly for companies of any size. Network attacks are easier to prevent than ever before!
Advanced Malware Protection (AMP) is a Multidimensional Savior
Cisco makes a whole range of networking products designed to create an all-secure network environment. The Advanced Malware Protection (AMP) is not a standalone feature; rather it involves a number of other Cisco features and functionalities.
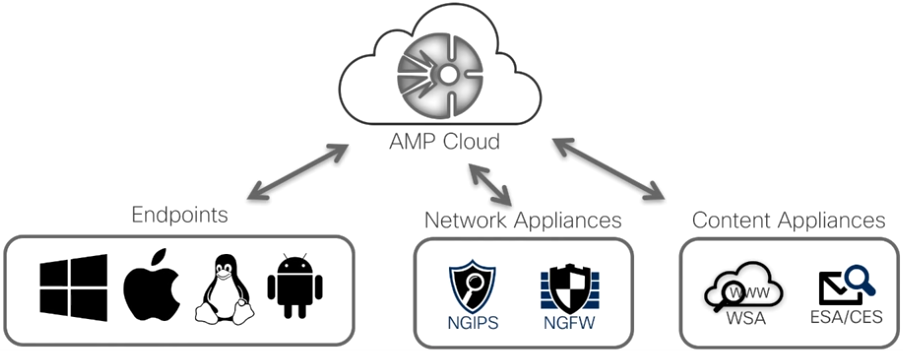
The goal is to provide a more connected network environment capable of self-detecting threats and relaying the characteristics of a threat over an entire network. Malware is more capable and smarter every day; so until all the endpoints in a network know about a threat (e.g. malware) safety can’t be guaranteed. In the Cisco AMP environment, all AMP endpoints in the network including network and content appliances relay on the Cloud to share intent providing full awareness. Whenever one network endpoint is aware of the nature of a potential attack, all other endpoints receive the information through AMP cloud. The ecosystem is proactive and takes over a lot of control to keep the IT security leaders in a company worry-free.
With Cisco AMP, network security does not necessarily have to be a complicated responsibility any longer.
Cisco Advanced Malware Protection
Learn how AMP for Endpoints helps to prevent breaches as well as quickly detect and respond to the most advanced cyber-attacks.
How Cisco AMP Deals with Network Threats
All networks in Small Business or large Enterprises are prone to attacks, especially enterprise networks. Cisco AMP treats every potential breach scenario in three phases – pre-attack, during-attack, and post-attack.
- Pre-Attack: AMP enabled Cisco endpoints monitor all incoming and outgoing traffic thoroughly. For most of the known threats that exists on the vast internet, this initial screening should be enough. However, malware are now smarter than ever and capable of disguising themselves as something more innocent, therefore, an endpoint not connected to a cloud based security environment would not likely be able to distinguish the suspicious activity. Cisco’s on-board Sandbox monitors any file that does not look right and alerts all other endpoints about the threat.
- During-Attack: Known or new, a Cisco AMP enabled network infrastructure eliminates all threats in real time. As the AMP enabled endpoints in an established network talk to each other in through Cisco Unity Connection for enterprise connections, the alert message of a potential ongoing attack is relayed across all active endpoints in the network.
- Post-Attack: Once Cisco AMP prevents an attack, the cloud is updated with relevant behavioural data of the attack that just took place. Cisco Talos, a full time ‘network intelligence’ group that works on network security would then look into the matter, analyse the scenario, replicate the attack with their 1100+ decoy devices and threat traps and provide the customers with a comprehensive report on how to stay secure while connected to the internet. Issuing patches for endpoints might be one possible step against network intrusions, in necessary cases.
Top Security Concerns:
If your security concerns are any of the following, Cisco AMP Everywhere is the ideal solution for your business:
- Securing Today’s Data Center
- Simplify, Automate and Innovate
- Mobility and Secure Access
- New and Emerging Threats
- Cloud Security
- Eliminate Your Blind Spots
- Ransomware
Cisco AMP Endpoints:Continuous Analysis and Retrospective Security
Learn how Cisco AMP for Endpoints provides continuous analysis of files and retrospective security. Monitor and record file activity at all times to quickly catch malicious behavior.
How AMP and Unity Go Hand-in-Hand
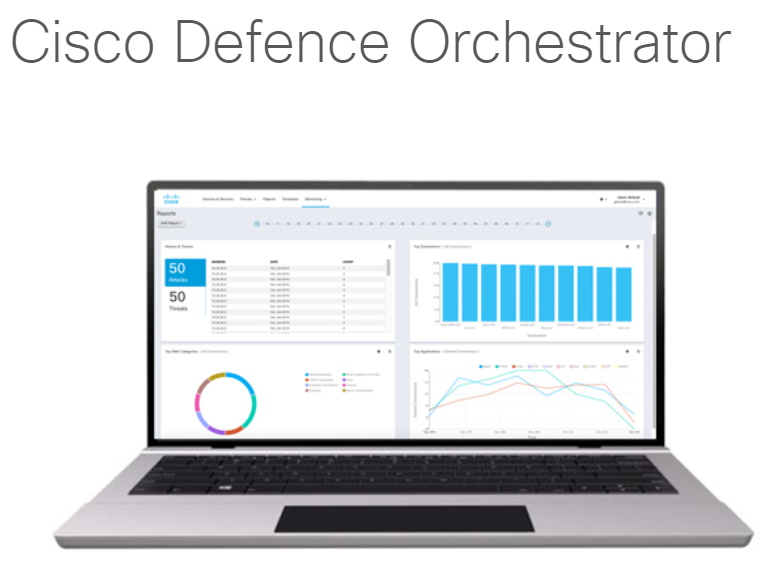
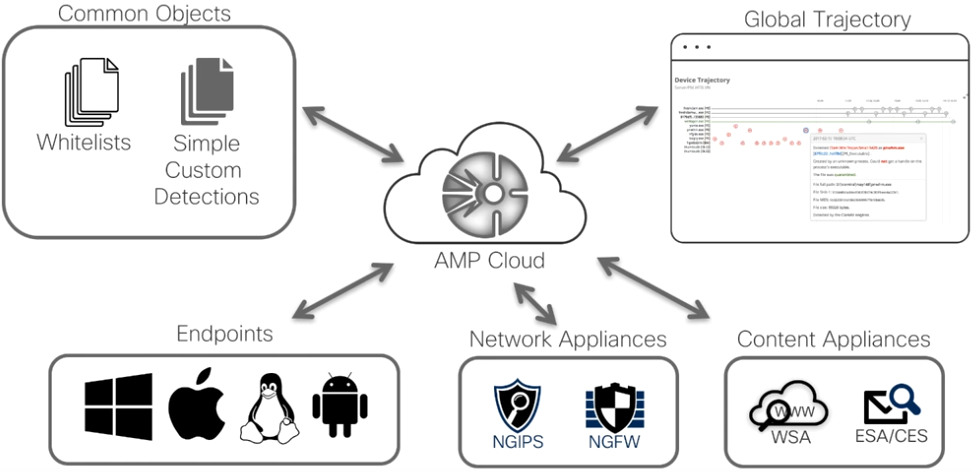
In other words, the new AMP Unity platform is what enables the IT security personnel in any network to effectively manage a network of any size, scale the network up or down, and enforce security policies on any end. Briefly, the Cisco AMP Unity offers the following features:
- Configuring whitelist and blacklists and enroll these policies across a wide range of enterprise endpoints from one console, without physically working on each endpoint.
- All feedbacks are synchronised to AMP cloud, which acts as a bridge among the endpoints, network appliances like NGIPS and NGFW, content appliances like WSA and ESA/CES, and the Cisco network Global Trajectory.
- Monitoring all gateways in one console – web browser, emails, video gateways etc.
- Controlling outbreaks, that is, actually eliminating the network threat. Manually destroying the threat is only a few clicks away from the IT security personnel should they choose to do so, or the whole thing can be set to act automatically upon detection of any network intrusion or attack.
- The person in charge of the network can generate custom reports manually on threat detection and elimination for further assessment inside or outside the organisation.
Is this the Future of Network Security?
A cloud based network security environment that learns on its own is certainly the way to go. Networks consisting of hardware from different vendors that cannot talk to each other, or are not manageable through one single console are so outdated by 2018’s standards. Seeing the bigger picture ahead of time and efficient methods of acting fast are the major requirements for network safety in 2018 and Cisco AMP for endpoints does just that.
Don’t leave your Business exposed, one of our engineers can setup a Free Trial and get protected from day one using Cisco AMP, for more info contact us.
Cisco Threat Response Demo
Threat Response automates integrations across select Cisco Security products and accelerates key security operations functions: detection, investigation, and remediation. It is a key pillar of our integrated security architecture.