Pxosys Achieves Cisco Advanced Security Specialization
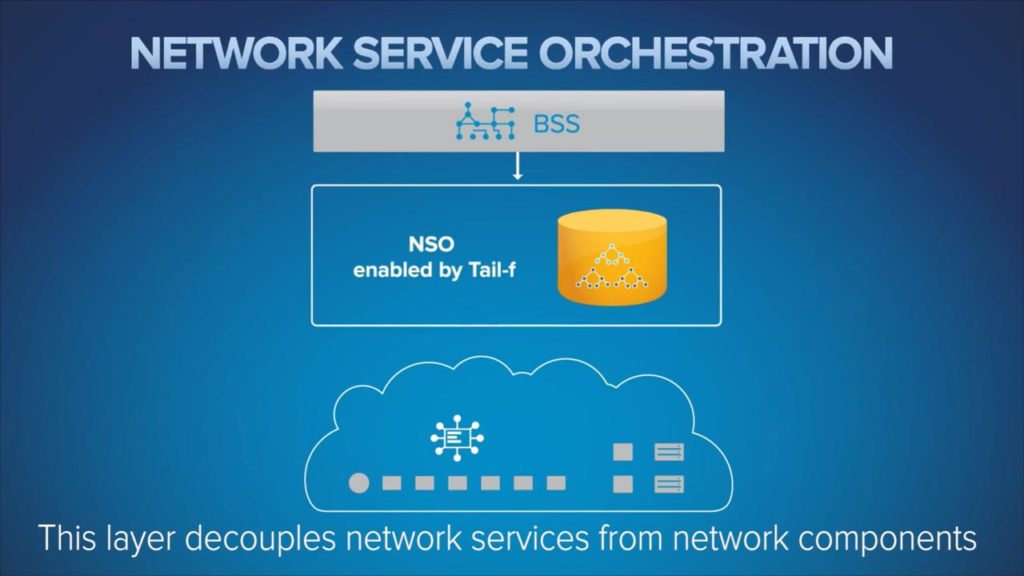
Cisco Security Architecture Specialization assesses the ability of a Partner to deliver to scope, design, install, and support Cisco products, technologies and solutions that are under Cisco’s Security Architecture.