Router IP Traffic Export (RITE), or simply IP Traffic Export, is a method of copying traffic directly from a router to an external device, such as a Protocol Analyzer or an Intrusion Detection System (IDS). This feature can be used to replace SPAN/RSPAN configurations deployed on L2 ports/VLANs. Two main benefits of RITE is, first, the ability to duplicate the traffic received on a WAN interface, such as Serial port, and second, granularity of our configuration – we can be very selective in what traffic will finally get copied from the network.
Before we discuss the configuration of RITE, just few words about limitations of this feature :
- The device receiving the exported traffic must be in the same L2 network as the router’s interface (e.g. must be directly connected). This interface is known as “outgoing” in the RITE’s terminology
- This (outgoing) interface must be an Ethernet port. Incoming interface(s) (where the traffic is received and optionally sent through) can be anything (e.g. WAN/LAN)
- Traffic generated by the router configured for RITE cannot be exported
A sample topology for RITE may look like one below. Our monitoring station (PC) is directly connected to R2’s RITE outgoing interface, Gig0/0 :
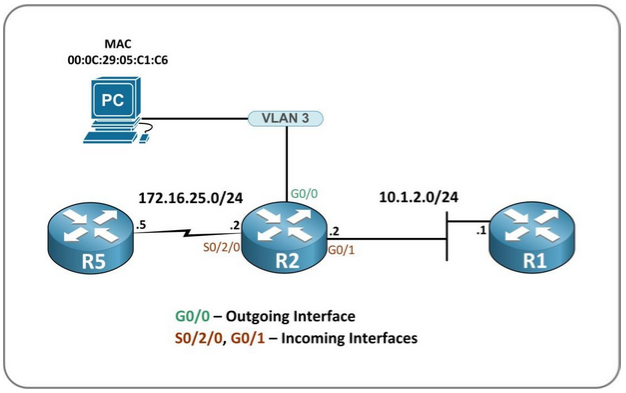
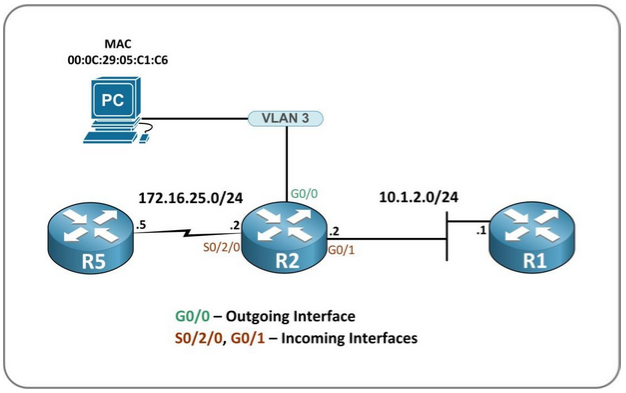
Now when we know what RITE can do for us, let’s take a look at a configuration example. I will be using the topology above as a reference.
The configuration of IP Traffic Export is very straightforward – it is all about creating a Profile and applying it to a monitored interface. In our case, we will configure two different profiles to show you how certain settings affect the traffic which is copied.
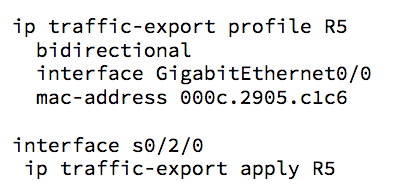
Let’s say that our first goal is to copy the traffic sent from or destined to R5. We can easily accomplish that by configuring a RITE Profile and applying it to interface S0/2/0 (so this will be our “incoming” interface) :
By default only traffic incoming to the port gets copied (don’t confuse this with an “incoming interface”, which is what we monitor). This is why I specified the “bidirectional” option – it causes the router to export both, incoming and outgoing traffic on the monitored interface. Next step was to specify what is our “outgoing” interface (“interface”) – again, one through which the copied packets will be sent. This is obviously G0/0, the port connected to our PC (with Network Analyzer turned on), which MAC address is 000c.2905.c1c6 (“mac-address”). Finally I activated the Profile by applying it to the incoming interface, S0/2/0.
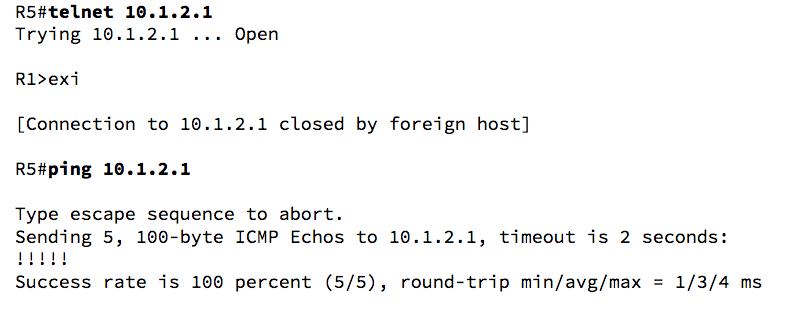
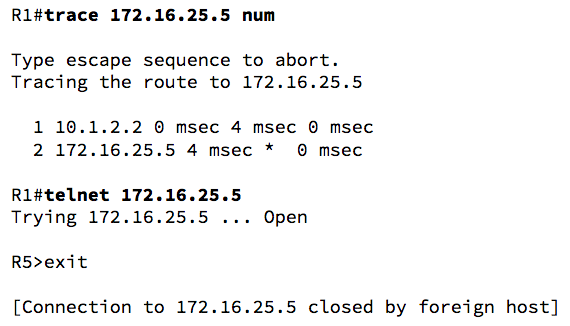
Let’s test this configuration :
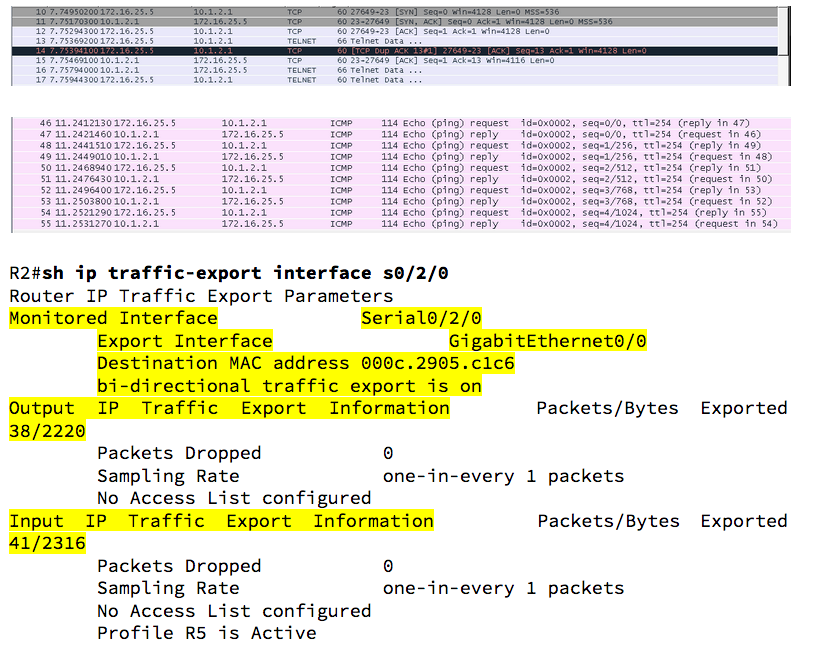
Here are the results (Telnet, then ICMP) :
Note that not only the traffic from R5 was exported, but also replies from R2 – it is because we configured the “bidirectional” keyword in the Profile.
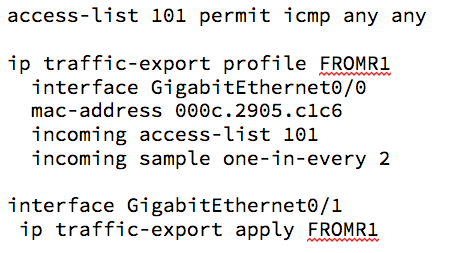
Next, let’s say we are only interested in traffic coming TO the G0/1 port – we only want to copy the traffic coming from R2. In addition, we will say we only want to copy ICMP packets, just one every 2 (50% of the traffic received on the port). Here’s how we can do that :
OK, what changes here? We did not use the “bidirectional” keyword, so we are only looking at the incoming packets. The “incoming access-list” command was used to tell the router what do we want to copy (specifically the ACL referenced in this command), and “incoming sample one-in-every” says how many packets we want to export (one in two here).
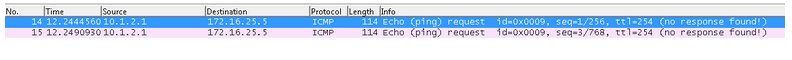
We see only two packets got copied, as expected, and no replies were received :